Workaround for Ting MMS bug
The Problem
I’ve been a happy Ting customer for years. I recently found out that Ting users can only send and receive MMS messages over 3G. If you are connected to 4G, no dice. This is not a big deal to me – who sends MMS anymore? Turns out my wife’s friends and family do. So, I looked into it.
The solution
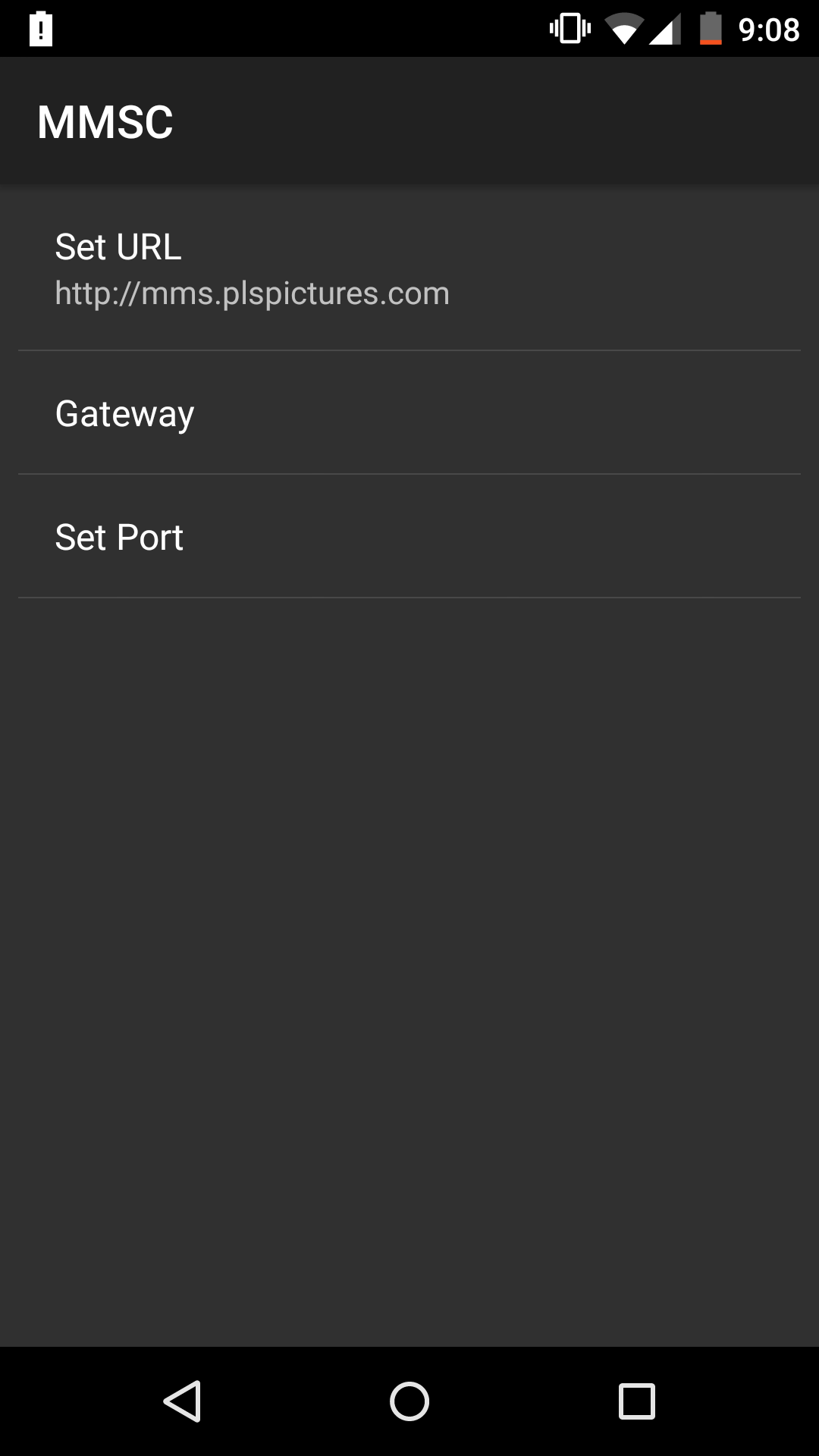
The fix is pretty simple: disable your MMSC proxy by clearing it out. You can read how to edit your MMSC settings on the Ting MMS Troubleshooting page.
Why it works
Normally when you send or receive MMS messages on Ting/Sprint, data flows through two servers: a proxy server and an end server.
The proxy server restricts which phones/computers can access the MMS service by enforcing a source IP whitelist. When requests pass through the proxy, a token (presumably used for authentication) is added to them and they are forwarded onto the end server. The end server then does its magic and your message is delivered.
It seems that right now the proxy is misconfigured: it doesn’t accept traffic from the Ting/Sprint 4G LTE network.
The solution works because the end server doesn’t check the token – you can send requests directly to it and it will process them as if they passed through the proxy. If you remove the proxy server from the communication path, the source IP restriction goes with it. Problem solved.
Aside
After a quick google it looks like most MMS servers aren’t too concerned with security, but this kinda drives home how easy it would be spam the world with something like the StageFright exploit. All you need to spoof an MMS is a valid phone number – not too difficult to guess one of those.