The old Flickr slideshow app and the White House
TL;DR
The old Flickr slideshow app is still online and it contains a hard-coded exception to its location-tracking logic for viewers of the Obama-Biden campaign and White House-related accounts.
The app contains logic to track the geolocation of everyone except viewers of the whitehouse and change.gov streams
Background
NibbleSec/Minded Security posted a well-written description of a simple attack based on CVE-2011-2461 to r/netsec on Tuesday of this week. The article outlines a method to submit credentialed requests on behalf of a (victim) user of a website that hosts a vulnerable Adobe Flex Flash application.
As luck would have it, I was able to use the attack against a client during a penetration test on Wednesday. Since I had all the pieces necessary to probe for the bug and develop a custom exploit handy, I decided to poke around public websites that welcome white-hat pen testing for other instances of the vulnerability that evening.
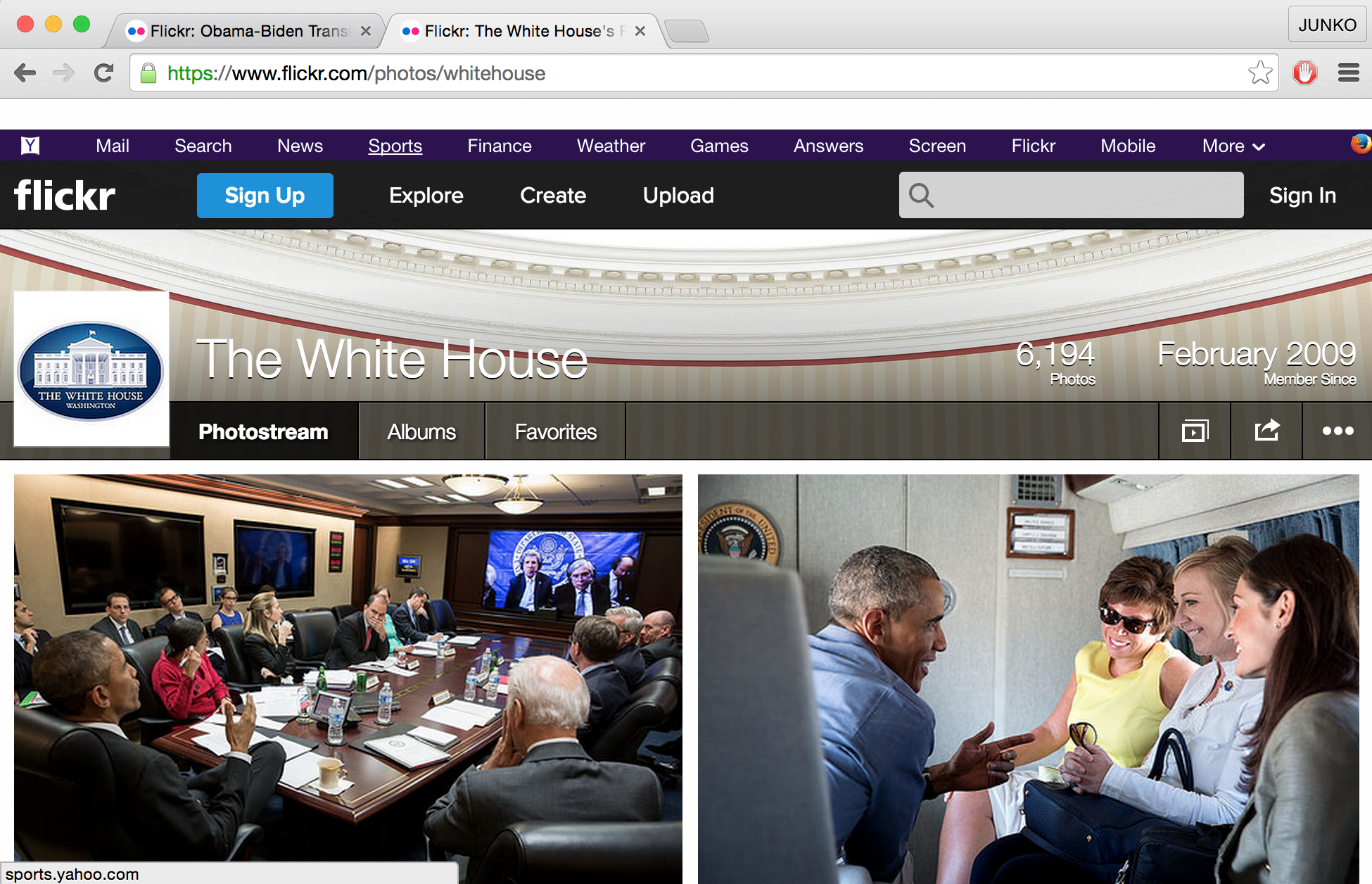
The Flickr Slideshow app
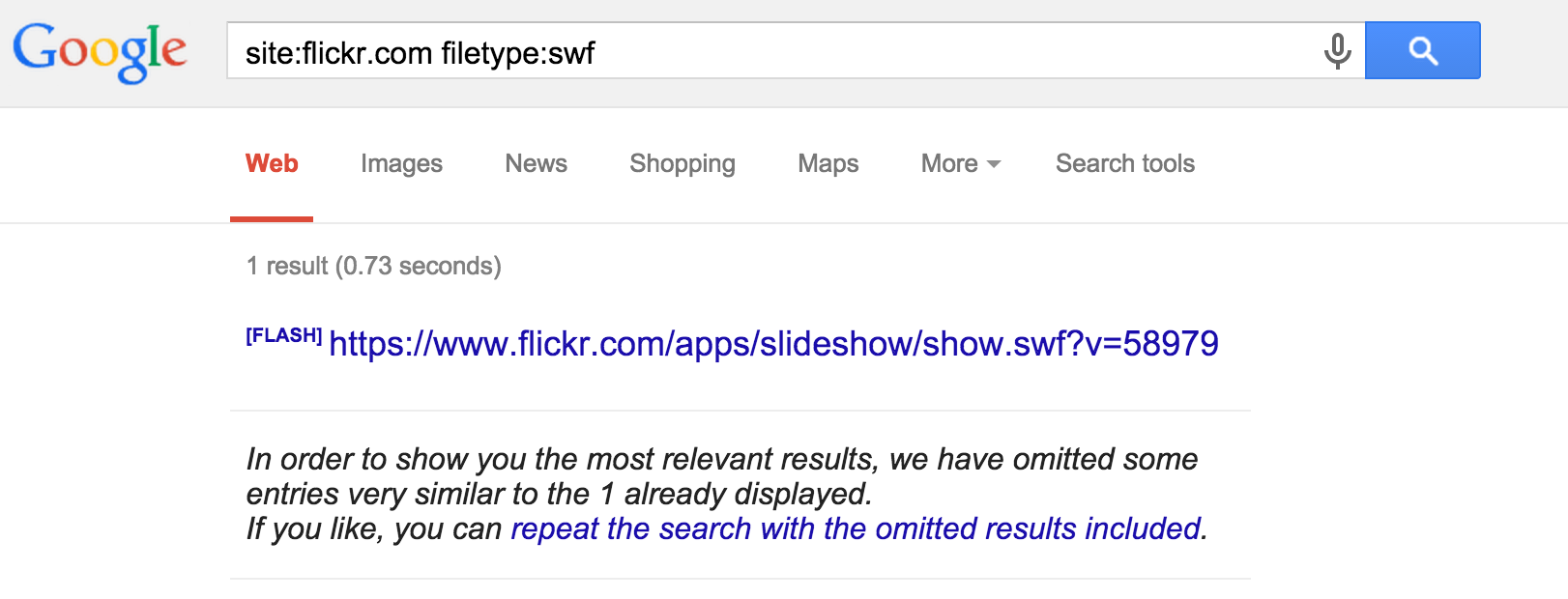
One of those websites was Flickr. There are a few old SWFs on their whitehat-friendly domains but none of the hosted files that I came across were vulnerable. Along the way, however, I came across something odd.
Leet hacking
My quick Google dork turned up two media player apps. I wasn’t sure what they were at first, but additional searches based on the file names revealed a handful of forum posts describing what they are and how to use them.
While they weren’t vulnerable to NibbleSec’s attack, the apps seemed to be old and somewhat broken in their own right. I decided to give them a once-over to see if they contained any obvious vulns that could lead to credentialed access to user sessions (or worse).
SWFs contain ActionScript
Most SWF files simply contain plaintext ActionScript along with some media and other data (file format spec is here). Users can decompress SWFs using OS-supplied tools and view their contents manually, but there are several downloadable and web-based tools that will do it for you.
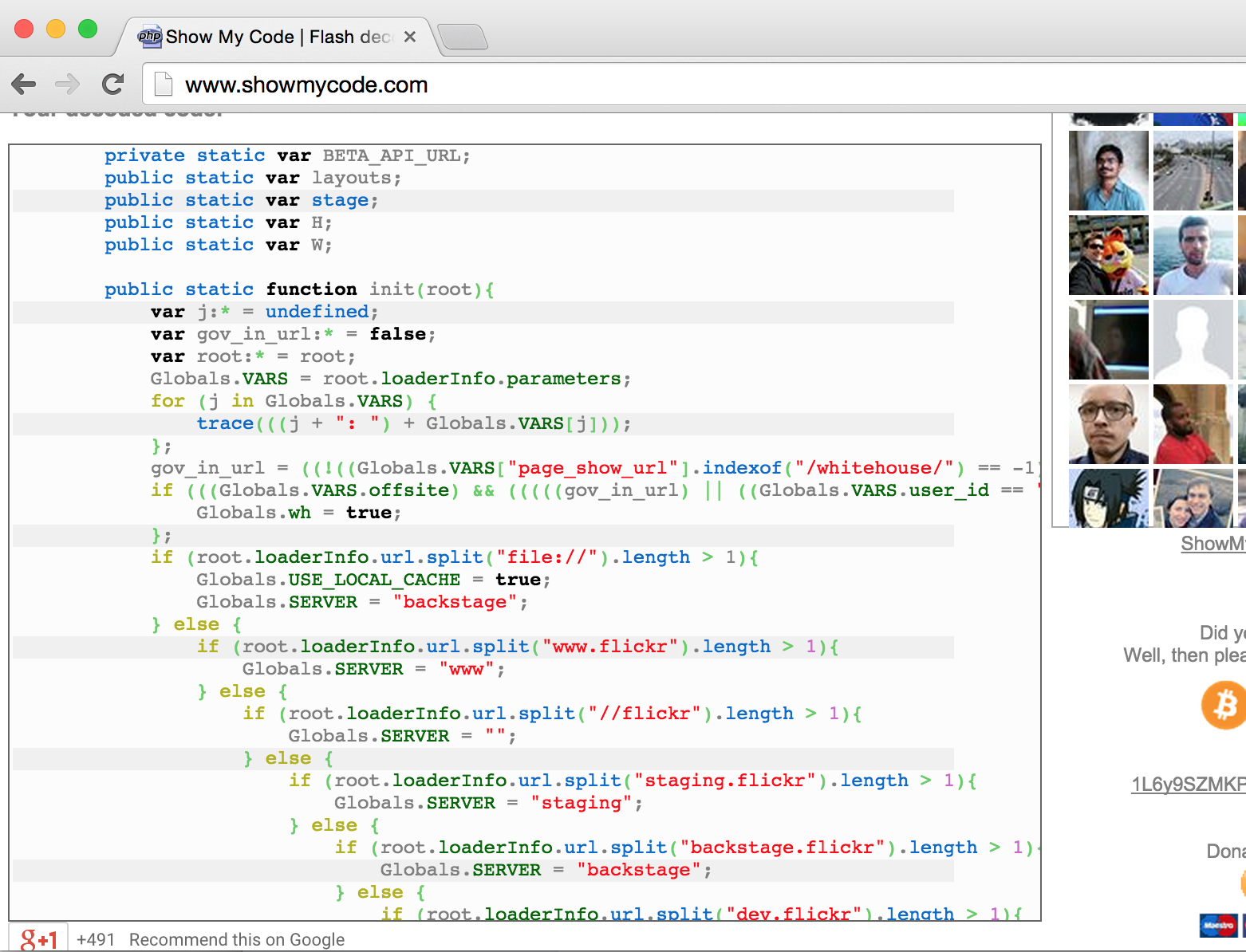
So, I decided to give the URL of the old Flickr slideshow app to ShowMyCode.com to take a peek at the ActionScript.
No file downloads required
Identifying Obama-Biden and Whitehouse media viewers
After loading the URL, my eyes were immediately drawn to a few lines in the init() function:
gov_in_url = ((!((Globals.VARS["page_show_url"].indexof("/whitehouse/") == -1))) ||
(!((Globals.VARS["page_show_url"].indexof("/changedotgov/") == -1))));
if (((Globals.VARS.offsite) && (((((gov_in_url) ||
((Globals.VARS.user_id == "32284207@N05")))) ||
((Globals.VARS.user_id == "35591378@N03"))))))
{ Globals.wh = true; };
The ActionScript in this file is pretty ugly, but the strings above stuck out. The script is setting a global var if the app user is viewing a slideshow whose Flickr URL contains “whitehouse” or “changedotgov”. The other two conditions above refer to the Flickr user IDs for those accounts. Such hack.
The change.gov account
Tracking location, and other special treatment
The Globals.wh flag set in the logic above is used in a few other places in the code. Cosmetically, it looks like some logos are stripped from the top bar of the app and a subtitle is removed from the end screen when it is set:
if (!(Globals.wh)){
this.addChild(this.logo);
this.addChild(this.logo_small);
} else {
this.logo.width = 0;
this.logo_small.width = 0;
};
...
if (!(Globals.wh)){
this.addChild(this.sub_title);
};
The interesting part appears in the go_go_go function, which gets called after initialization. Aside: this file is chock-full of whimsical variable names and spaghetti code.
if (!(Globals.wh)){
this.callBeacon();
};
The callBeacon function looks like this:
function callBeacon(){
var id:*;
var type:*;
var bugLoader:Loader = new Loader();
if (Globals.VARS.offsite){
id = 792600329;
type = "p";
} else {
id = 792600328;
type = "b";
};
bugLoader.load(new URLRequest((((((
(Globals.PROTOCOL + "://geo.yahoo.com/") + type) + "?s=") + id) + "&t=") + new date().gettime()
)));
}
After a quick search on the domain above (geo.yahoo.com), my guess is that this logic constitutes cutting-edge IP-based geolocation tracking technology from Yahoo (circa 2008).
So, putting it all together, in addition to some UI tweaks the deprecated Flickr slideshow app contains hard-coded logic to geolocate all users, except those who view photos from the Whitehouse and Obama-Biden streams.
Probably not a conspiracy… but maybe!
It is common practice for modern web applications to track user geolocations, and it was probably common practice back in the 2007-2009 timeframe when the old Flickr slideshow app was presumably developed as well.
But, the fact that the app contains hard-coded logic to avoid tracking users of these specific accounts strikes me as kind of weird. Maybe the accounts were so popular that the tracking requests were overwhelming some backend analysis system. Maybe the government voiced concerns about divulging the President’s location. Maybe the coder was just screwing around and figured no one would notice. Or maybe…
$ git blame show.as
f4a35aa8 (Joe Biden 2007-11-27 10:30:38 -0500 17) gov_in_url = ..
Feel free to post your thoughts and conspiracy theories below, hit me on twitter, etc.
Thanks for reading.